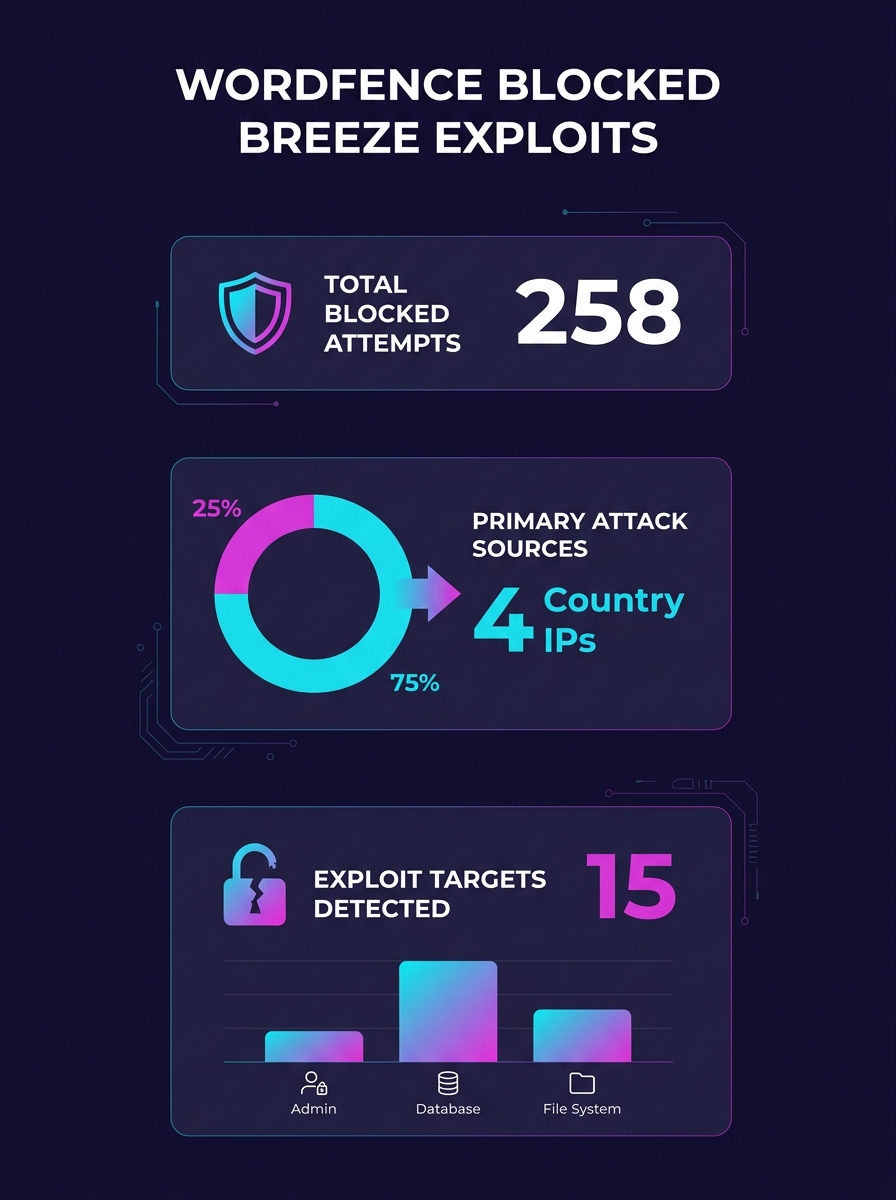
Attackers began exploiting a critical Breeze Cache plugin vulnerability within hours of its public disclosure April 22nd, targeting the arbitrary file upload flaw across an install base of 400,000 WordPress sites, according to Wordfence. The security firm blocked over 30,000 exploit attempts in the two weeks following disclosure.
The vulnerability allows unauthenticated attackers to upload arbitrary files, including PHP backdoors, and achieve remote code execution on affected sites. Breeze Cache's vendor released a fully patched version April 21st, one day before Wordfence published the vulnerability in its Intelligence database.
Wordfence's data shows exploitation began the same day the flaw became public knowledge, demonstrating the narrow window agencies have to patch client sites before attackers move.
Attack Surface Expands Across Agency Client Portfolios
The arbitrary file upload flaw represents a code-execution path that bypasses authentication entirely. An attacker can upload malicious PHP files to a vulnerable site without credentials, then execute those files to establish persistent access. Wordfence classified the vulnerability as critical based on this attack vector.
The 400,000-installation figure places Breeze Cache in the mid-tier of WordPress plugin adoption. Agencies managing dozens or hundreds of client sites face a patch management challenge whenever a popular plugin releases a security update. The timeline between patch release (April 21st) and active exploitation (April 22nd) compressed the response window to effectively zero for agencies that rely on manual update processes.
Wordfence's firewall blocked the initial wave of attacks for sites running its protection, but agencies without centralized security tooling across their client portfolios would need to identify affected sites and deploy the patch individually.
Patch Status Creates Audit Requirement
The fully patched version shipped April 21st, but agencies must verify installation across all client sites. WordPress plugins do not auto-update by default unless an agency has configured managed updates through MainWP, ManageWP, or similar tools.
Sites running outdated versions of Breeze Cache remain vulnerable to the file upload exploit. Wordfence did not publish version numbers for the vulnerable and patched releases in its disclosure, but the firm confirmed the patch closed the arbitrary upload path.
Agencies that previously experienced plugin vulnerabilities compromising client sites have adopted centralized dashboards to track plugin versions across portfolios. The Breeze Cache incident reinforces the operational requirement for real-time visibility into plugin status.
The 30,000 blocked exploit attempts Wordfence recorded suggest automated scanning tools added the Breeze Cache flaw to their attack databases immediately after disclosure. Agencies cannot assume a multi-day grace period between vulnerability publication and active exploitation.
Agencies Implications
Agency operations teams must audit client sites for Breeze Cache installations and verify patch status before the end of this week. The April 22nd exploitation timeline means vulnerable sites have been exposed for two weeks as of publication. Agencies without centralized plugin management should prioritize implementing MainWP, ManageWP, or InfiniteWP to track updates across client portfolios in real time.
The incident highlights a structural risk in white-label WordPress infrastructure: agencies inheriting legacy client sites may not have complete plugin inventories. A vulnerability audit requires scanning staging and production environments for Breeze Cache, not just checking a remembered plugin list. Agencies should run wp-cli plugin list or equivalent commands across all sites to generate definitive inventories.
For agencies scaling white-label operations, the Breeze Cache exploit demonstrates why security patching cannot operate on ticket-based schedules. Vulnerabilities disclosed on Tuesday are exploited by Wednesday. Agencies need either automated patch deployment with rollback procedures or dedicated security monitoring contracts that guarantee same-day response to critical CVEs. The alternative is explaining to clients how their site got backdoored through a known flaw your team had two weeks to patch.