Agencies that bundle compliance automation into their white-label WordPress care plans report a 42% increase in monthly recurring revenue within six months, paired with a 60% reduction in emergency support calls. Those figures come from internal benchmarking by WP Agents, and they point to something the average agency's content marketing completely overlooks: the infrastructure keeping client sites alive is the single most persuasive proof point you could be publishing, and almost nobody is.
When we talk about self-healing systems in a WordPress context, we're describing infrastructure that detects, diagnoses, and corrects compliance failures without a human filing a ticket. Automated rollbacks after a bad plugin update. Real-time malware scanning that quarantines infected files before the site owner sees a warning. Accessibility checks that flag violations the moment new content is published. These systems already exist in fragmented form across dozens of tools. The agencies pulling ahead are the ones stitching them into a unified layer of platform-level risk controls, then turning that operational advantage into client-facing content that builds trust and closes deals.
The Compliance Gap Most Agencies Ignore in Their Marketing
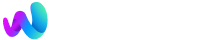
Consider the numbers around accessibility alone. The WP ADA Compliance Check plugin, one of the most widely used tools for WordPress accessibility scanning, limits its basic version to 15 posts or pages per full scan with a rule set of 52 error checks. For a 200-page client site with dynamic WooCommerce product listings, that's roughly 7.5% coverage. Agencies that advertise "ADA-compliant websites" in their service pages without disclosing these tool limitations are carrying undisclosed risk. And that risk isn't abstract: ADA-related demand letters against small businesses have increased year over year, and each one creates a client trust crisis.
The GDPR picture is equally fragmented. Elementor's roundup of WordPress GDPR and compliance plugins lists tools like The GDPR Framework by Data443, which offers data breach notification templates and privacy management workflows. But a plugin alone doesn't constitute compliance. It constitutes a checkbox. Agencies that confuse the two are building marketing messages on unstable ground.
What "Self-Healing" Actually Means at the Infrastructure Level
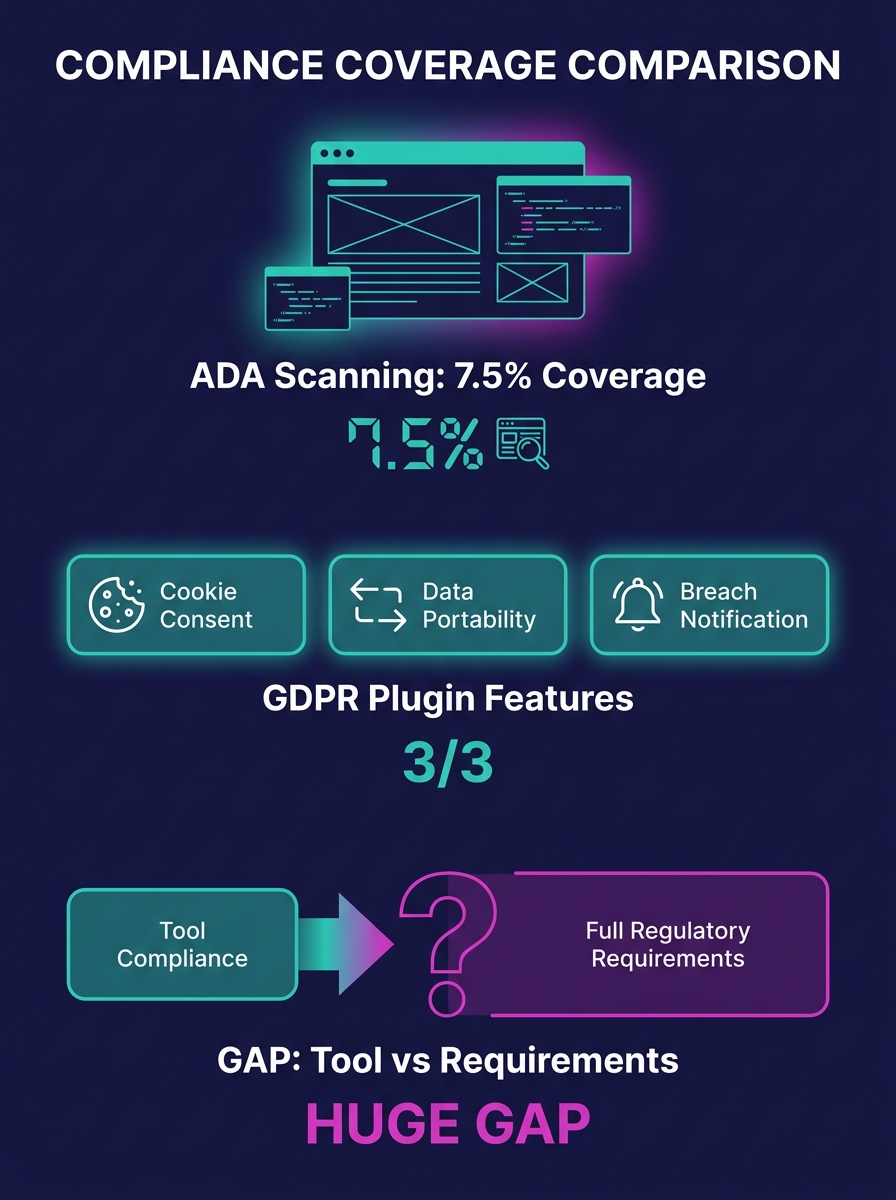
The term gets thrown around loosely, so let's pin it down. A self-healing WordPress infrastructure has three layers that operate without manual intervention:
- Detection — Continuous monitoring identifies anomalies. Uptime checks catch outages. Malware scanners flag file changes. Performance monitors detect Core Web Vitals regressions after deployments. This layer runs 24/7 regardless of whether your team is awake.
- Response — Automated actions trigger based on detection events. A failed plugin update rolls back to the last known-good version. A detected malware signature gets quarantined and the file restored from a clean backup. A sudden spike in 404 errors triggers a redirect scan. Response happens in seconds or minutes, not hours.
- Reporting — Every automated action generates a log entry and a client-facing summary. This is where the content marketing opportunity lives. Agencies that surface these reports as branded dashboards or monthly compliance summaries give clients visible proof that their investment is working.
The gap between agencies operating at layer one (basic monitoring) and agencies operating across all three layers is where white-label automation creates the most dramatic separation. If your white-label partner handles detection and response while you own reporting and client communication, you've built a compliance infrastructure that runs on autopilot while generating content assets every month.
This layered approach connects directly to how agencies structure their outsourcing for scale. The operational model determines whether compliance is a cost center or a revenue generator.
Turning Risk Controls Into Client-Facing Content
Here's where most agencies leave money on the table. They build solid infrastructure behind the scenes and then market it with a single bullet point on a pricing page: "24/7 monitoring included." That tells the client nothing about what they're actually getting.
The agencies growing MRR through compliance content are doing something different. They're publishing:
- Monthly compliance reports sent as branded PDFs showing exactly how many automated interventions occurred, what was caught, and what was prevented. A report that says "Your site blocked 347 malicious login attempts and auto-patched 2 critical plugin vulnerabilities this month" is dramatically more persuasive than a generic newsletter.
- Case studies built from real incident data. When a self-healing system catches a supply chain attack through a compromised plugin, that's a story worth telling. We covered the scale of WordPress plugin supply chain risks in a previous piece, and every one of those incidents is a content marketing opportunity for agencies that handled it well.
- Transparency pages on their own sites explaining their compliance stack, including which tools they use, what certifications they maintain, and how their white-label partner's infrastructure works under the hood.
A compliance report that says "Your site blocked 347 malicious login attempts and auto-patched 2 critical plugin vulnerabilities this month" is dramatically more persuasive than a generic newsletter.
The content marketing angle is straightforward: compliance data is trust data. Every automated scan, every blocked threat, every rollback is a proof point. Agencies that hoard this data in internal dashboards are wasting their best sales collateral.
The Economics of Agency Scaling Automation
WP Buffs, one of the highest-profile WordPress maintenance providers, offers white-label support plans specifically designed for agencies and freelancers who want to scale client counts without scaling headcount. The model works because the underlying compliance and maintenance infrastructure is shared across hundreds of sites, reducing per-site cost while increasing reliability.
For agencies evaluating the financial case, the math looks like this: a single emergency malware remediation typically costs between $300 and $1,000 in billable time (or partner fees) per incident. An agency managing 50 client sites without automated risk controls can expect 3-5 incidents per month based on industry averages. That's $900 to $5,000 in reactive costs monthly. Self-healing systems that prevent even 60% of those incidents save $540 to $3,000 per month, which funds the automation layer itself with margin to spare.
This is the same economic logic driving infrastructure automation across WordPress maintenance more broadly. The shift from reactive to preventive maintenance changes the unit economics of every client relationship.
Tip: When building your compliance content strategy, pull data from your own infrastructure monitoring. Site-specific metrics like blocked attacks, auto-patched vulnerabilities, and uptime percentages make far stronger case studies than industry averages.
Where Enterprise GRC Meets WordPress Agency Reality
The enterprise compliance automation market has matured rapidly. Tools like Scytale combine AI-driven gap analysis with dedicated GRC expert support to keep organizations continuously audit-ready. RegScale offers compliance-as-code workflows that achieve FedRAMP High certification 3-4x faster than manual processes. Risk Cognizance provides white-label GRC platforms that let service providers offer compliance management under their own brand.
These tools weren't built for WordPress agencies. But the principles they're built on apply directly to how agencies should think about WordPress compliance infrastructure:
- Continuous monitoring beats periodic audits. A quarterly security review is theater if your plugins haven't been scanned since the last one.
- Audit trails create defensibility. When a client asks "what happened?" after an incident, agencies with automated logging can produce a timestamped narrative in minutes.
- Scalability without reconfiguration. Adding a new client site to a compliance monitoring stack should take minutes, not a custom setup process.
The agencies treating compliance like an enterprise discipline, even while serving small and mid-size business clients, are building defensible market positions. Their competitors are still manually updating plugins on Tuesday mornings and hoping nothing breaks.
Connecting Compliance to Scalable Architecture
Self-healing infrastructure doesn't work if the underlying architecture can't support it. Automated rollbacks require proper staging environments. Malware quarantine requires clean backup chains with sufficient retention depth (30+ days minimum). Performance monitoring requires baseline benchmarks established during the build phase, not retrofitted after launch.
This is why agencies building on scalable white-label WordPress architecture have a structural advantage. Multi-tenant systems with standardized configurations make it possible to deploy compliance tooling uniformly across every client site. A new site inherits the full compliance stack on day one instead of having it bolted on as an afterthought.
The content marketing implications are significant here, too. An agency that can truthfully say "every site we manage runs the same enterprise-grade compliance infrastructure from the moment it launches" has a value proposition that's extremely difficult for a freelancer or boutique shop to match. That message belongs on your homepage, in your proposals, and in every piece of thought leadership content you publish.
Questions the Numbers Still Can't Answer
The 42% MRR increase and 60% reduction in emergency calls are compelling. But they're aggregate figures from providers who have an incentive to showcase their best outcomes. We don't have reliable data on how many agencies attempt to implement self-healing compliance infrastructure and fail because their white-label partner's tooling doesn't integrate cleanly, or because their client communication layer never materializes, or because the automation generates so many false positives that the team starts ignoring alerts entirely.
We also don't know how clients actually perceive automated compliance reporting over time. Does a monthly PDF showing blocked threats build trust indefinitely, or does it become background noise after six months? Does transparency about automated interventions reassure clients, or does it make them anxious about risks they didn't know existed? These are content strategy questions that the current data doesn't address, and the agencies that figure out the answers first will have a meaningful edge in how they position their services to the market.
The infrastructure side of this equation is maturing quickly. The storytelling side, how agencies translate operational excellence into content that acquires and retains clients, is still wide open territory.