A high-severity vulnerability in MonsterInsights, one of WordPress's most popular analytics plugins, allows authenticated attackers with basic subscriber access to steal live Google OAuth tokens and reset advertising integrations, according to a CVE disclosure published May 12.
CVE-2026-5371 affects all versions of MonsterInsights up to and including 10.1.2. The flaw carries a CVSS score of 7.1 out of 10, placing it in the high-severity category. Agencies managing client WordPress installations that use MonsterInsights for analytics tracking face immediate exposure.
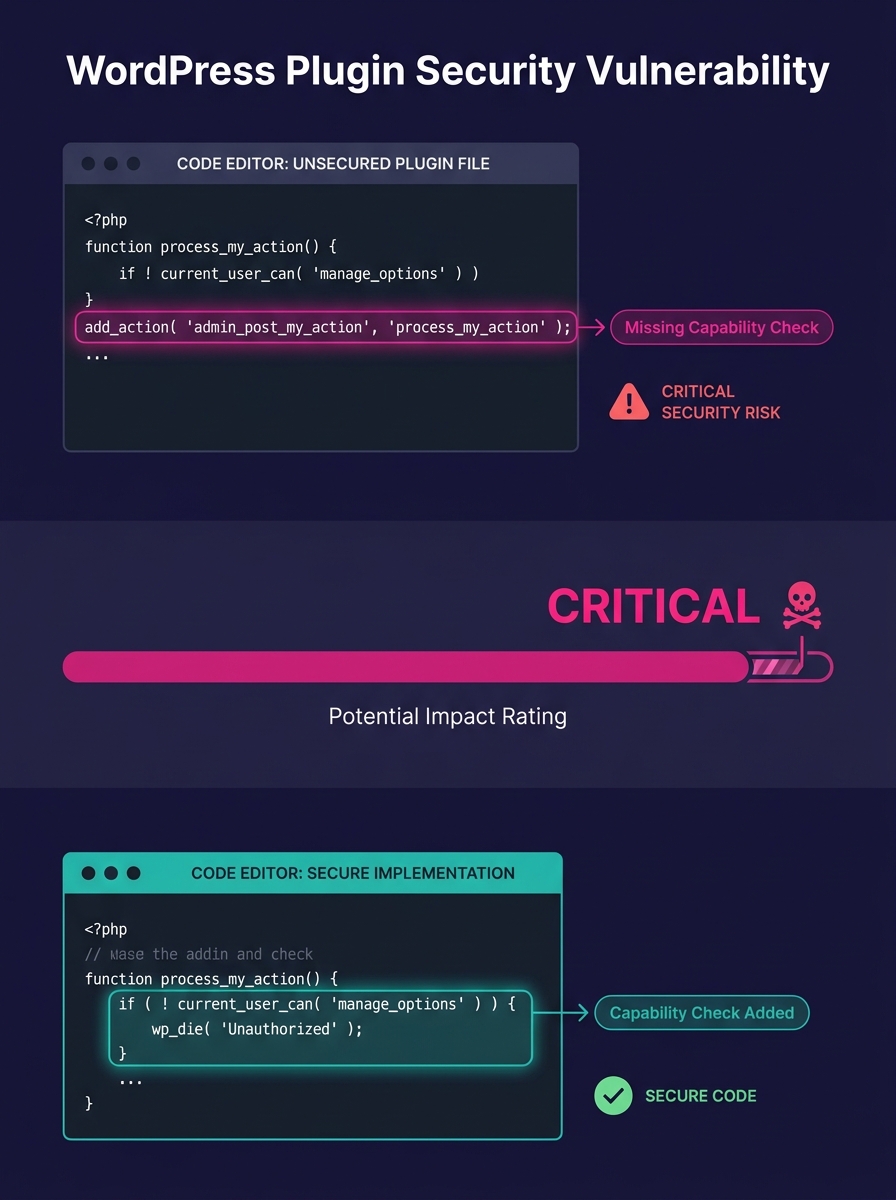
Missing Capability Checks Create Attack Vector
The vulnerability stems from missing capability checks on two functions in the plugin's codebase: get_ads_access_token() and reset_experience(). These functions control access to Google OAuth credentials and Google Ads integration settings.
WordPress's role hierarchy assigns subscriber as the lowest authenticated access level. Users at this tier typically have permission only to manage their own profile. The missing checks allow anyone with subscriber-level credentials—including compromised accounts or malicious users granted basic access—to retrieve active Google OAuth access tokens without administrator privileges.
The disclosure notes attackers can also reset the plugin's Google Ads integration, disrupting analytics tracking and advertising campaigns. Sites running affected versions face the same supply-chain risks documented in broader plugin compromise patterns.
Technical Details and CVSS Vector
The Common Vulnerabilities and Exposures database classifies the attack vector as network-exploitable with low complexity. The CVSS breakdown shows high confidentiality impact and low integrity impact, with no availability disruption expected.
Attack complexity remains low because exploiting the flaw requires only valid subscriber credentials. No user interaction is necessary once an attacker gains authenticated access. The scope remains unchanged, meaning the vulnerability affects only the plugin's own security boundary rather than escalating to broader WordPress core access.
Wordfence's threat intelligence database lists the vulnerability alongside reference links to the affected code in MonsterInsights version 10.0.3. The vulnerable functions appear in the plugin's admin-assets.php file and the Google Ads integration class.
Patch Status and Affected Installations
The CVE disclosure does not specify whether a patched version has been released. The vulnerability report indicates versions through 10.1.2 remain vulnerable as of the May 12 disclosure date.
MonsterInsights markets itself as "Google Analytics Dashboard for WordPress (Website Stats Made Easy)" and maintains significant market share among WordPress analytics plugins. Sites using the plugin to connect Google Analytics and Google Ads campaigns face token exposure if running vulnerable versions.
Agencies managing white-label WordPress builds with MonsterInsights installed should audit version numbers across their client base. Automated bot campaigns frequently target outdated plugins through credential attacks, making subscriber-level compromise a realistic threat vector.
What Happens Next
Agencies running MonsterInsights on production client sites should check version numbers immediately and prepare to deploy patches as soon as the vendor releases an update. Sites on version 10.1.2 or earlier require remediation.
In the interim, site administrators can restrict subscriber account creation and audit existing subscriber-level users for suspicious additions. Revoking Google OAuth tokens and regenerating credentials provides temporary protection against token theft, though this breaks existing analytics connections until tokens are reissued post-patch.
White-label development teams managing multiple client installations should add MonsterInsights to their patch-monitoring workflow and prepare client communication explaining the OAuth token exposure risk. The vulnerability's network-exploitable classification and low attack complexity mean exploit code could circulate quickly once the CVE gains attention in attacker communities.